|
|
|
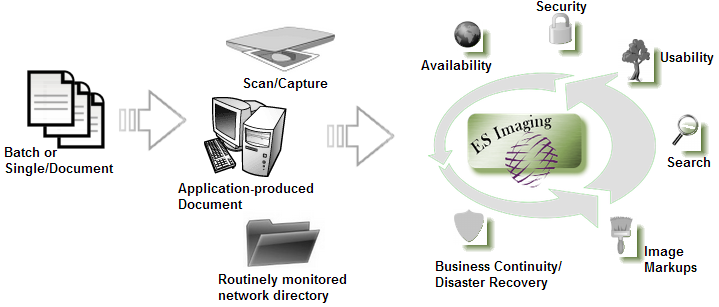
- Non-proprietary software allows access to any type of file
- Pages can be scanned via any WIA or TWAIN compatible scanner
- Digital pictures can be captured from any WIA compatible digital camera, web cam, etc.
- Emails can be imported from any POP email server (Yahoo Plus, Gmail, Exchange Server, etc), and searchable by subject, from, to, date, message, etc.
- Files can be streamed down for real time usage (movies, sound files, etc)
- Documents and images are accessible from remote locations via web browser
|
|
- Permissions are flexible and controlled by Administrator
- Manage with users or groups
- May be incorporated at any level (document or folder)
- Various security levels are supported for read-only/update access
- Audit information is retained for each document
- Files can be stored with AES 256-bit encryption for additional protection
- Reports available to assist with permission management
|
|
- Familiar tree structure tailored to your organization's specific needs
- Icons are customizable to your preference/organization
- Customizable keyword drop down lists
- Data integrity assurance by requiring keywords
- Document folders specific to your organization's needs
- Keyboard shortcuts available for many functions
- Can save versions of files with descriptive names
|
|
- On index values (keywords) using wild card search
- Full-text searching available when utililizing OCR
- Routine searches can be saved for later re-use
- Can be performed with either simple or complex criteria ('and', 'or', 'like', 'equals', '<', etc).
- Search at any parent folder or sub-folder document levels
|
|
- Supports scaling and rotation
- Redaction, popup notes, text overlays, circles, highlights, freehand drawing
- Can attach searchable note(s) to a folder or file
- Can permanently apply markups, by flattening image/file
|
|
- Ensure documents are safe in cases of flood, fire or other disasters
- Store documents on an external network for an extra security measure
- Return to normal business operations immediately after a disruption
|
|
- Route documents to workflow queues for approval, rejection, etc.
- Robust and flexible event system to handle any business rule or situation
- Over 25 different event types such as: sending emails, reading emails, changing keywords, moving documents, auditing, searching, importing/exporting, mathematical calculations, etc.
- Administrators can control anything in the system with event triggers driven by conditions
- Chain multiple events together and trigger them either with specific actions (saving, deleting, etc.) or on a schedule (daily, hourly, etc.).
- Scheduled events can be executed on demand
|
|
- Supports Windows 2000+ (2003, 2008, NT, XP, ME, Vista, 7, 8, 10, etc)
- Supports Linux and Mac OS X
- Supports iOS 4.3+ mobile devices (iPhone and iPad)
- Supports Android 2.3+ mobile devices with ARM v7 processors
- Open database design to allow system integration and external reporting
- Image formats directly viewable: PDF, PNG, JPEG, GIF, TIFF, BMP, JPEG 2000, FPX, PNM
|
© Copyright 2017 Everlast Software, LLC. All Rights Reserved.